Introduction
In cybersecurity, code review is the process of reading application source code with an attacker’s mindset to identify vulnerabilities that may never surface during black-box testing.
Unlike traditional peer code review (which focuses on readability or performance), security code review asks:
- What assumptions does this code make about user input?
- What trust boundaries are crossed?
- What happens if this function is abused, not used as intended?
Code review is where you stop guessing and start knowing.
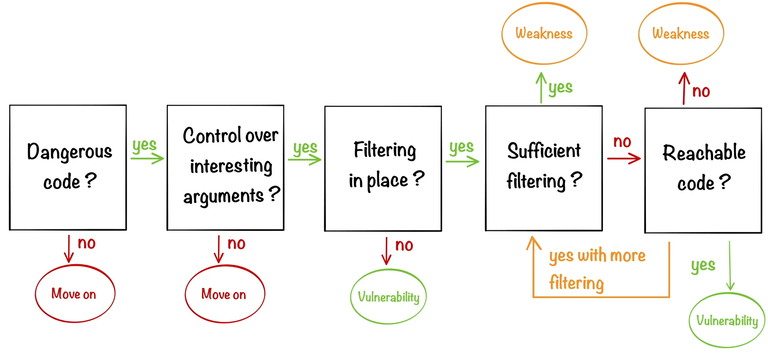
Below diagram from the source notes shows how someone can perform a code review by tracing the flow of data from input to output.
Why A Hacker Must Learn Code Review
1. Black-box testing has limits
Some vulnerabilities are:
- Logic-based (authorization, business rules)
- State-dependent
- Hidden behind feature flags or rare code paths
You’ll never fuzz your way into those reliably.
Code review lets you:
- See all execution paths
- Understand intended vs actual behavior
- Spot bugs before they become exploitable endpoints
2. Code review turns theory into certainty
In black-box:
“This might be an IDOR”
In code review:
“This endpoint checks
user_idfrom request body without ownership validation”
That difference matters in real reports, CTFs, and bug bounties.
3. You learn how vulnerabilities are born
Every major class of vuln becomes obvious in code:
- SQLi → string concatenation
- XSS → unsafe sinks
- IDOR → missing authorization checks
- SSRF → user-controlled URLs
- Deserialization → untrusted object input
Once you’ve seen it in code, you’ll recognize it instantly in live apps.
4. It makes you dangerous with very little access
With:
- Partial source code
- Decompiled JS
- Backend snippets
- Error stack traces
You can reconstruct how the app works internally and attack precisely, not blindly.
What Code Review Gives You That Scanners Never Will
| Scanners / Black-box | Manual Code Review |
|---|---|
| Pattern-based | Context-aware |
| Surface-level | Deep logic flaws |
| Misses auth issues | Finds privilege abuse |
| High false positives | High confidence |
| No intent | Understands intent |
Scanners don’t understand business logic. Humans do.
Common Vulnerability Classes Best Found via Code Review
Authentication & Authorization
- Missing role checks
- Trusting client-side claims
- User-controlled identifiers
- Broken multi-tenant isolation
Business Logic
- Discount abuse
- Free upgrades
- Replayable workflows
- State machine bypasses
Input Handling
- Partial validation
- Validation after use
- Type confusion
- Trusting framework defaults
Crypto Misuse
- Hardcoded secrets
- Weak randomness
- Reused tokens
- Homegrown crypto
Tools of the Trade
Static Analysis & Grep-Based
ripgrep (rg)grep,sed,awk- Semgrep
- CodeQL
- SonarQube (enterprise environments)
Language & Framework Knowledge
Knowing the framework is often more important than the language:
- Django / Flask
- Express / NestJS
- Spring Boot
- Laravel
- Rails
Vulnerabilities hide in framework misuse, not syntax.
Supporting Tools
- IDEs with call-hierarchy (VS Code, IntelliJ)
- AST explorers
- Dependency analyzers
- Git diff tools
But remember:
Tools assist the reviewer but they don’t replace them.